Bluetooth Device -: Bluetooth is a wireless technology that allows two different devices to connect. Every Bluetooth device has one or more profiles installed. These profiles determine what the device is capable of, such as “Hands-Free” (mobile headsets) or “Human Interface Device” (computer mouse). Bluetooth devices also work on the same frequency on which wi-fi does, and that frequency value is – 2.4GHz. Although, wi-fi also works on 3.6GHz and 5GHz frequency.
Hello my all dear Visitors, welcome again in this domain (www.bittutech.com). We can learn various technical topics and ethics of hacking to enhance your thinking ability and learning capacity. from here, we can also learn the various programming language or scripting languages to develop your own websites such as – HTML, CSS, PHP, and some languages are under-publishing.
What can we do with Bluetooth devices?
Table of Contents
First of all, I want to ask you a question – Why you use the Bluetooth device? either Your answer is – Transferring your document from one device to another wirelessly or Your technical answer is – share your 48–bit unique key with others to transfer or receive the file or heterogeneous document.
Various things were hidden behind the above technical answer, did you recognize them or not.
Ok don’t worry, I am going to explain these points in detail with an example of How scans all nearby Bluetooth devices and How to choose your victim’s Bluetooth device to get the essential information from it.
I’ll explain all basic points within an example but before we go ahead, we should know about some necessary pre-requisites and follow them to be uninterrupted among the example.
Prerequisites -:
- Operating System – Kali Linux (latest version)
- Bluetooth Adapter (External or Internal)
- Some essential Bluetooth scanning tools – hciconfig, hcitool, sdptool, btscanner.
Start the real journey to hack the Bluetooth device
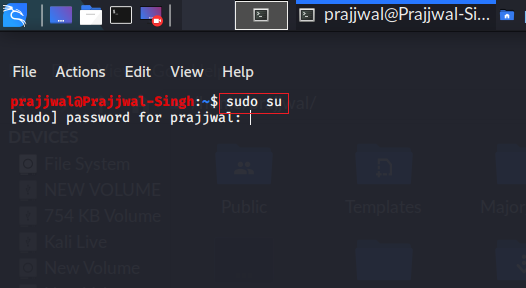
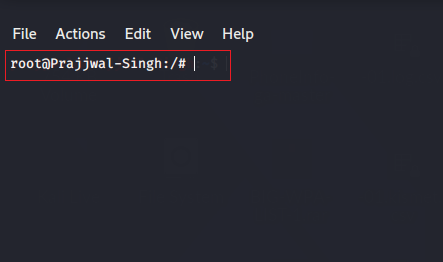
First of all, we should start our terminal window on our kali Linux machine, and type “sudo su” to get the permission of root access or permission of the administration. This command will give you the authority of root access to use all commands without assigning the sudo command before.
Type Command -: sudo su
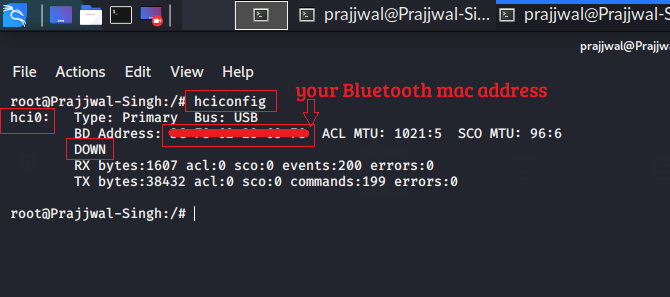
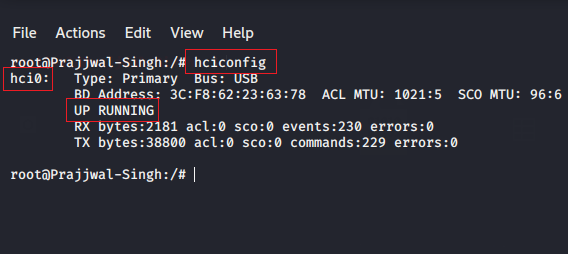
Step 1: Find your Bluetooth adapter name
Before going ahead, we should know about what is the name of our Bluetooth adapter?
Without knowing the name of our adapter, we can’t do it any operations, because with the help of name of adapter, we will send some racons during scanning time. Let’s start our Bluetooth engine to scanning all nearby devices.
/*some commands that you have to type into your terminal window. */
First command - "hciconfig" (for bluetooth configuration)
and the below command is for running up your Bluetooth adapter to scan all nearby Bluetooth devices.
Second command - "hciconfig hci0 up" (for enable the
monitoring mode)
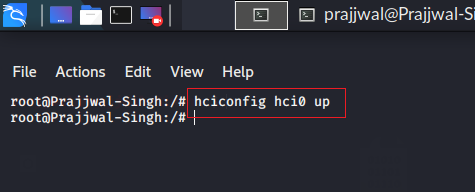
Type again “hciconfig” to check your adapter is in UP Running state or not.
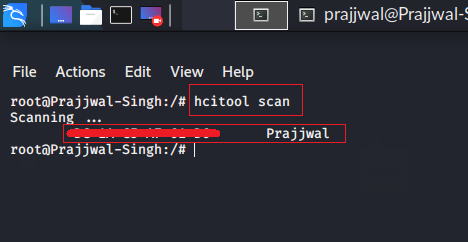
Step 2: Scan the nearby Bluetooth devices
So now, we are going to use an ultimate tool for scanning the nearby Bluetooth devices by sending racons packets all around. This tool gives us the result to form the device name and its Bluetooth mac address. This tool is pre-installed on your latest kali Linux version, name of this tool is -: “hcitool” and some of the attributes that will represent on your screen when you type from the keyboard “man hcitool“.
Typing “hcitool scan” command on the terminal window to represent all of the nearby Bluetooth devices that is enabled.
Type the Command -: hcitool scan
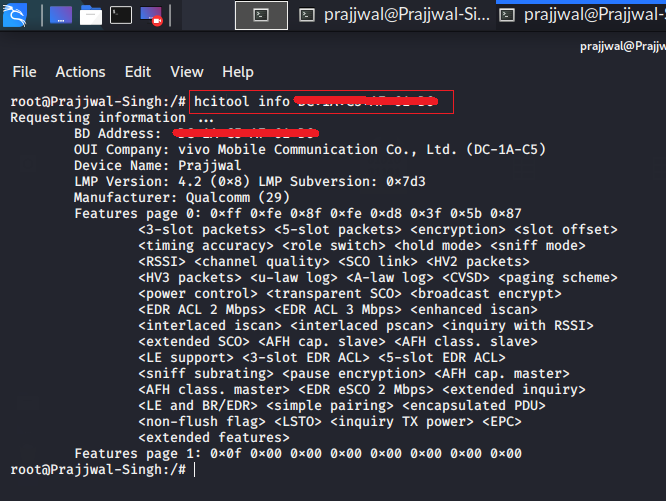
Step 3: Gathering all the information of Victim’s Bluetooth device
Choose the Victim’s mac address and type the following command to knowing about all information of victim’s Bluetooth device.
Syntax -: hcitool info <bdaddress>
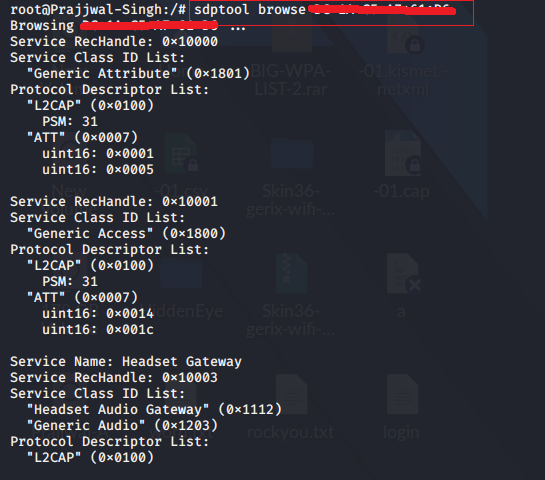
Use another tool to fetch all of the services of Victim’s Bluetooth Device
Use “sdptool” Tool to fetching and knowing about all of the service which is used by the Victim’s Bluetooth device. we can add and remove our local services to the Victim’s Bluetooth device to connect it.
Syntax -: sdptool browse <bdaddrss>
Use the Graphical Version tool for scanning all nearby Bluetooth devices
We can also use a graphical user interface to scanning and detecting the victim’s Bluetooth device with btscanner. btscanner is a graphical window tool to scan and inform all of the services which are used by the Victim’s Bluetooth device.
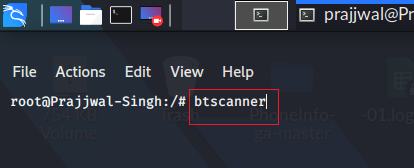
Type the “btscanner” command in your terminal screen and hit the enter button.
Read more hacking articles -:
- How to Split single Kali Linux terminal into multiple
- Top 10 Commands for Kali Linux Users || 2020
- How to Jam Wireless Network(Wi-Fi) with Kali Linux | 2020
- Advance Jamming: Jam Wireless Network using MDK3 tool with Kali Linux
- [Instagram Hack]|HiddenEye Hacking Instagram With Kali Linux 2020
- How to Hack Someone’s Wi-Fi Password with aircrack-ng tool
Last Words-: So my Dear Visitors, This is it, for now, we will meet very soon with another interesting article in this domain. you can join us on social networks to get the latest updates. I need your loving help and support to be motivated during writing the article.



Pingback: How to chat offline on WhatsApp: Disappearing Online Status
Pingback: How to record WhatsApp Video Calls, PUBG, Free Fire Games
Pingback: Top 5 Entertainment Apps for Android Users: Break from Study
Pingback: Why we need to learn programming language? >> bittutech